
Fundamentals of the dark web
By Angela Okeke-Ramos The internet is formed of multiple layers. Similar to the ocean only a fraction of these layers...

Teaching your Nanna about Cyber Security
By Eve Ferguson. Most grandparents are now joining the world of smartphones, social media, internet banking and following the global...
Users – The Weakest Link in Business Security Systems?
By Mustafa Obousy. Employees are proposed to be possibly the weakest link in a business in terms of its’ security...
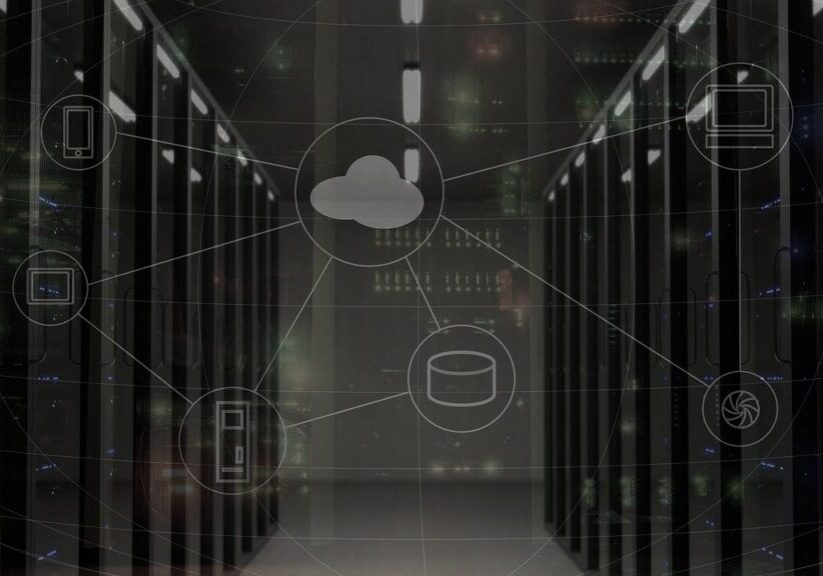
Is it Safe to use Serverless Applications?
By Bhaskar Deep. Let’s think like this, Storing our data at an unknown place. Is our data secure? can...

So, What’s Phishing?
By Amelia McGuigan (Cyber Security Student). After the fifth text message this week inviting me to click on a suspicious...

MageCart attack
By Atul Periwal. What is Magecart? Magecart is the name assigned behind the world's biggest cyber attacks to a...

Elevating security with virtualisation
By Anton Scott. Major operating systems such as Windows, Mac and Linux have never been as secure as some may...

Cyber crime against women
By Atul Periwal. Women play a key role in transformative cultural, environmental and social changes essential for sustainable development. Occupying...

Side-channel attacks
By Diana Ion. Too many times overlooked by common security measures, side channels can offer attackers new avenues for information gathering...

Data breaches: A story that seems to never end
By Farhan Subhan. Throughout our time on planet Earth, there have been major developments in nearly all aspects of life;...


