The Dyn DDoS: attacking the Internet’s global address system
By Tanzeer Hossein On October 21, 2016, one of the most significantDistributed Denial of Service (DDoS) attacks occurred. The target...
The Bangladesh Bank Heist
By Tanzeer Hossein The 2016 massive cyberattack on Bangladesh Bank, the central bank of Bangladesh, remains one of the most...

The Cyberattack on Tangerine Telecom
By Tanzeer Hossain In February 2024, Tangerine Telecom, a prominent Australian internet and mobile service provider, became the latest victim...

The Wannacry Incident
By Tanzeer Hossain In May 2017, a ransomware attack known as "WannaCry" caused a worldwide crisis, severely disrupting computer systems...
Asessing cyber risks
By Roddy Risk management is central to cyber security. It is impossible to create a fully secure system (even an...

The Equifax Breach
By Tanzeer Hossain In September 2017, Equifax, one of the largest credit reporting agencies, fell prey to one of the...

The SolarWinds Cyber Attack
by Tanzeer Hossain In December of 2020, the world witnessed one of the most sophisticated cyberattacks in history: the SolarWinds...

The Cost of Ignoring Low-Level Risks
By Roddy The British Library’s report on the cyber attack which it suffered in October 2023 contains some insightful points...

Passwords
By Roddy Passwords, pah! Old-fashioned, insecure. Don’t cha just hate ‘em? Well no, they’re OK, especially if handled thoughtfully and...

Active vs. Passive Cyber Security
By Roddy. There is a lot of confusing – or inconsistent - terminology in cyber security (‘Tactics’ in the MITRE...

Fundamentals of the dark web
By Angela Okeke-Ramos The internet is formed of multiple layers. Similar to the ocean only a fraction of these layers...

The value of mutual TLS for API authentication
By Robert Grigoras. The security and privacy of data exchanged between different systems through APIs is of utmost importance. API...

An honest review Of ‘Undeclared War’ On Channel 4
By Robert Grigoras. Introduction The series is set in 2024, The Undeclared War tracks a leading team of analysts buried...

Teaching your Nanna about Cyber Security
By Eve Ferguson. Most grandparents are now joining the world of smartphones, social media, internet banking and following the global...
Users – The Weakest Link in Business Security Systems?
By Mustafa Obousy. Employees are proposed to be possibly the weakest link in a business in terms of its’ security...
Is it Safe to use Serverless Applications?
By Bhaskar Deep. Let’s think like this, Storing our data at an unknown place. Is our data secure? can they...

So, What’s Phishing?
By Amelia McGuigan (Cyber Security Student). After the fifth text message this week inviting me to click on a suspicious...

MageCart attack
By Atul Periwal. What is Magecart? Magecart is the name assigned behind the world's biggest cyber attacks to a multinational...

Elevating security with virtualisation
By Anton Scott. Major operating systems such as Windows, Mac and Linux have never been as secure as some may...

Cyber crime against women
By Atul Periwal. Women play a key role in transformative cultural, environmental and social changes essential for sustainable development. Occupying...

Side-channel attacks
By Diana Ion. Too many times overlooked by common security measures, side channels can offer attackers new avenues for information gathering...

Data breaches: A story that seems to never end
By Farhan Subhan. Throughout our time on planet Earth, there have been major developments in nearly all aspects of life;...

Why having the right toys matters?
By Diana Ion. It is common knowledge in the security community that it is not a question of “IF a...

Android wallpaper – a medium for malware infection
By Atul Periwal. You might be thinking of how a wallpaper can be a medium of malware? There might be...

Coronavirus: A cyber threat
By Atul Periwal. The outbreak of coronavirus (Covid-19) has halted the entire world for months and it’s not ended yet....

Coronavirus: Remember to stay safe online too
By Chloe Wood. It has been 99 days since Boris Johnson announced to the UK that we will be going...

Passwords and Paranoia
By Anton Scott. The issue with universal passwords We have all been there, midway through creating a new account for...

The importance of Ethical Hacking
By Shameer Sabar. As technology advances, and organisations incorporate more and more IT systems into their business in order to...

Minimising risk in business: the relevance of cybersecurity and data protection
By Ivan Seifert. Despite being a term on everyone’s lips and an increasing wealth of information becoming available online, cybersecurity...
Changing characteristics in private-public cybersecurity cooperation
By Kate Dinnison. 1. Techplomacy First came the creation of a U.S. Government ambassador to the Silicon Valley, then came...

Darkweb crack-down spurs digital refugee crisis
The FBI, DEA and Europol are celebrating the successful take-down of AlphaBay and Hansa, two of the Dark Web’s...

Interview with Dr. Tim Stevens, Lecturer in Global Security at King’s College London
By Kate Dinnison. Recently, we chatted with Dr. Tim Stevens, a lecturer in Global Security at King's College London. His...

Crash Override: Too big to ignore
By Kate Dinnison. Last December, hackers targeted an electric transmission station in Ukraine, causing approximately one-fifth of the city to...
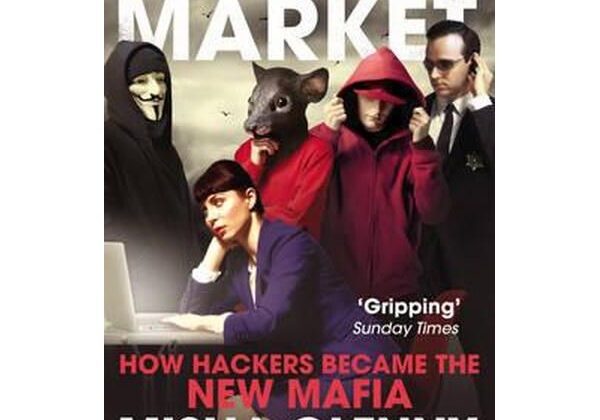
An interview with Misha Glenny, author of ‘DarkMarket: How Hackers Became the New Mafia’
By Kate Dinnison. We recently interviewed Misha Glenny, journalist and author of DarkMarket: How Hackers Became the New Mafia. His 2011...

Bitcoin: the risks and how to stay safe using it?
By Melissa Liow. Developed in 2009 by an unknown individual or group under the pseudonym Satoshi Nakamoto, Bitcoin was the...

Protecting yourself against Ransomware
By Joel Chang. If you've watched the news lately you will see ransomware, ransomware, ransomware all over the place. Some of...
Four recommended Cyber Security Summer reads
We’ve selected some celebrated books in the world of cyber security you should check out this Summer to expand your...

Your PC taken hostage
By Aqsa Hussain. We recently witnessed a cyber attack which left individuals and organisations virtually crippled. The WannaCry ransomware cyber-attack hit...

Personal Cyber Hygiene
by Kate Dinnison The Office for National Statistics estimates that there were 2.46 million cyber incidents and 2.11 million victims...

Decrypting the encryption debate.
by Kate Dinnison Encryption is essentially the process of turning information into code that prevents snoops, criminals, and spies from...

Risk in the Internet of Things
By Oliver Yule-Smith. Much of the current excitement on the Internet of Things (IoT) revolves around a focus on how...

Estonia: how the country became ‘poster child’ for national cyber security.
By Aqsa Hussain Estonia is considered one of the world’s most digitally advanced societies. Much of the country’s state and...

Who watches the watcher?
By Aqsa Hussain.. We have all heard about the whistleblowing scandal of 2013 which erupted in the USA resulting in...
Hipster counter-espionage?
By Philip Smedegaard It is now three years ago that the Russian Federal Protection Service (FSO) (in charge of protecting...

IOT – progress or cyber madness?
I was on the underground (train) recently, staring at the myriad of adverts that adorn the carriages. Amongst the adverts...

Hear no evil, see no evil – cyber awareness
What you don't know can't hurt right? Wrong! The issue with most organisations is that they are waiting for...

Phishing and the cost of your information
By Aqsa Hussain. Do you remember receiving that email some time ago mentioning ‘Here is an invoice to the flight...

Ethical Hacking vs Hacktivism: where perspective matters.
By Aqsa Hussain. What is ethical hacking? There are codes of conduct for almost every industry, from the rules of...

Distorted risk perception: Why we fear terrorism, but don’t worry about our cyber security.
By Ivan Seifert. What makes you feel safe? Perhaps locking your apartment door at night. Perhaps not walking alone through...

Security fatigue
  By Philip Smedegaard "Please update your password settings. Please enter a new password that does not include your birthday. Password...

Trusted security
How do you know that you are your mother's child? How can you be sure that the chef in that...

Secrets (and lies)
Phase 3 - The execution Somewhere in a call centre…. Call centre operative: Hello, helpdesk, how can I be of assistance?...



