The Bangladesh Bank Heist
By Tanzeer Hossein The 2016 massive cyberattack on Bangladesh Bank, the central bank of Bangladesh, remains one of the most...

The Wannacry Incident
By Tanzeer Hossain In May 2017, a ransomware attack known as "WannaCry" caused a worldwide crisis, severely disrupting computer systems...

The Equifax Breach
By Tanzeer Hossain In September 2017, Equifax, one of the largest credit reporting agencies, fell prey to one of the...

Teaching your Nanna about Cyber Security
By Eve Ferguson. Most grandparents are now joining the world of smartphones, social media, internet banking and following the global...
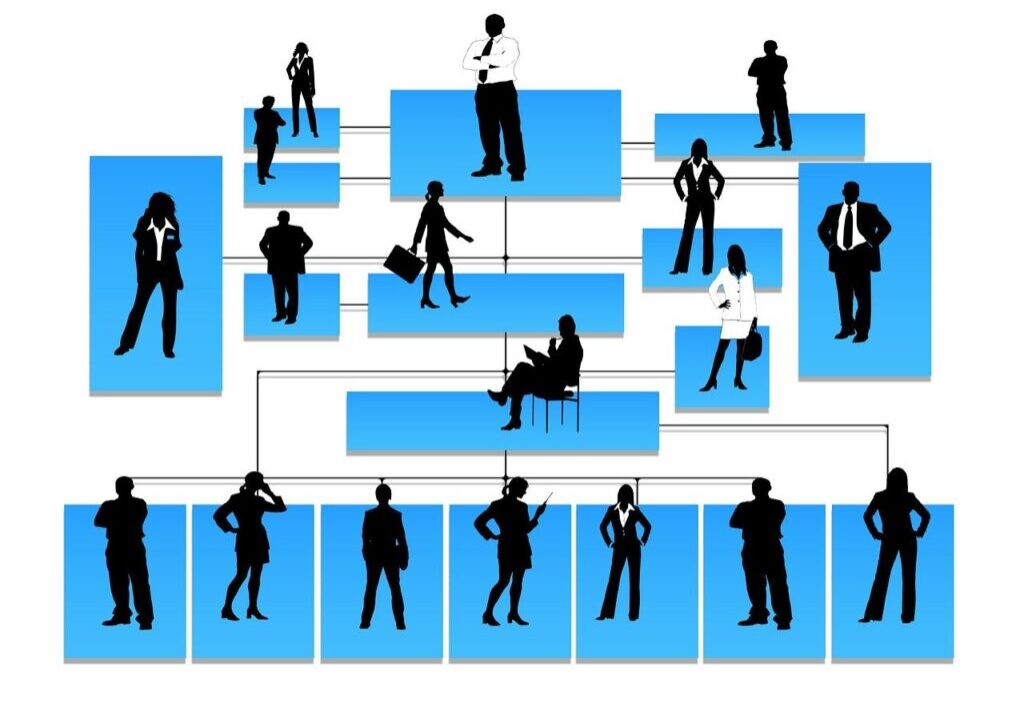
Users – The Weakest Link in Business Security Systems?
By Mustafa Obousy. Employees are proposed to be possibly the weakest link in a business in terms of its’ security...

So, What’s Phishing?
By Amelia McGuigan (Cyber Security Student). After the fifth text message this week inviting me to click on a suspicious...

MageCart attack
By Atul Periwal. What is Magecart? Magecart is the name assigned behind the world's biggest cyber attacks to a...

Cyber crime against women
By Atul Periwal. Women play a key role in transformative cultural, environmental and social changes essential for sustainable development. Occupying...

Data breaches: A story that seems to never end
By Farhan Subhan. Throughout our time on planet Earth, there have been major developments in nearly all aspects of life;...

Coronavirus: A cyber threat
By Atul Periwal. The outbreak of coronavirus (Covid-19) has halted the entire world for months and it’s not ended...